Exclusions are lists of items such as files, domains, and processes that VIPRE should ignore; in essence, telling VIPRE what not to scan.
Certain types of software can be impacted by antivirus programs. Some software may experience strange behavior. For example, processes may be blocked by the antivirus programs based on behavior traits exhibited by the software; file lock contention may occur during scans; and so on. This is especially common with certain categories of software such as server software, databases, data backup, key loggers, and more that either require exclusive access to specific files or that use files that, although benign, contain patterns that antivirus software sees as suspicious.
How Exclusions Work
Exclusions are communicated from VIPRE to the agents as part of the policy. As the agents protect your devices, the exclusions are applied.
VIPRE provides an initial set of exclusions that is applied to all devices for resources that we know to be potential issues. Our own virus definition files, for example, would lead VIPRE to believe it had found malware if it were not excluded.
Administrators can create custom exclusions to accommodate the specific needs of their organization. Exclusions are defined in an exclusion list. That list is then associated to one or more policies (scope=policy). Alternatively, a list may be associated to all devices (scope=site).
Exclusion lists provide the flexibility to define exclusions once, and apply them to as many policies as required.
What to Exclude
Knowing what needs to be excluded from antivirus is not always intuitive. Sometimes VIPRE will tell you it blocked a process or quarantined a file that you know to be benign; in this case you can simply add that program or file to the exclusion list. In other cases, however, software may not work correctly for non-obvious reasons.
When first deploying, consider the following
- Test - deploy to a group of test devices for your environment
- Monitor - perform normal activity on the test systems to determine if VIPRE blocks or impacts application behavior - you may need to disable VIPRE to determine if it is the cause of any observed odd behavior
- Research - look for vendor recommendations for third-party software used in your organization. Some vendors maintain a specific list of resources to exclude for antivirus programs. For example, Microsoft maintains a Microsoft Anti-Virus Exclusion List for their software.
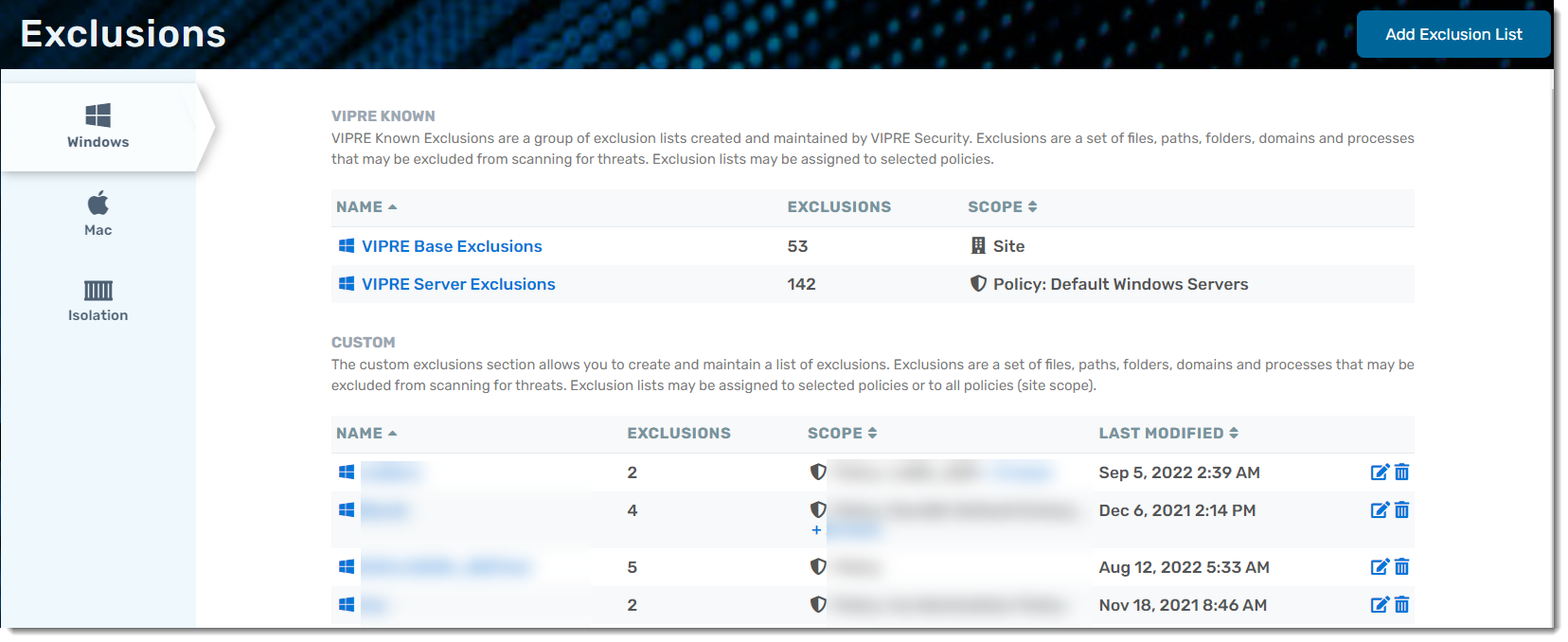
Predefined and Custom Exclusions
Exclusions are viewed and managed from the Exclusions page. Custom lists can be created for Windows and Mac policies. For Windows based policies, a VIPRE Known list is provided.
- VIPRE Known - read-only exclusions for Windows OS that come with VIPRE, curated by the VIPRE Team. VIPRE manages both the default VIPRE Base Exclusions and VIPRE Server Exclusions lists. We push out additions to these exclusions that work across our entire customer base.
- Custom - any lists of exclusions that you create
Your instance of VIPRE EDR comes with VIPRE Base Exclusions, which applies to all of your Windows devices. Additionally, VIPRE Server Exclusions is automatically assigned to Windows Servers (through the Windows Servers policy, one of the default policies included with VIPRE Cloud).
As suggested in this article, the need to create custom exclusions is a common practice when using antivirus software. When adding exclusions, be sure to follow your vendors' specific recommendations. Note however that excluding resources at a higher level than what is recommended can be a security exposure. For example, do not exclude items at the directory, or folder, level when the vendor lists specific files in the folder.
Adding Custom Exclusions
Before adding an exclusion list, verify your exclusion type in the left-side light-blue navigation bar, as options expand.
- Click Add Exclusion List in the top right corner
- Name your custom exclusion list and click Next
Once you're in the custom exclusion list, you can create exclusions. Select an exclusion category below to see available options:
Windows
When creating an Exclusion List, you can select one of five types that are specific to Windows: File, Domain, Process, Hash, and Device. You can also select the scope of your Exclusion List, choosing Site, meaning the list will apply to all of your Windows endpoints at the site-level, or Policy, meaning the list will apply only to endpoints that belong to any policies you've selected to be associated.

- Click +Add Exclusion at the top-right corner of the screen
- Select one of five exclusion types:
- File: Choose a Subtype (Filename, Filepath, or Folder), and add Value (see example in text box)
- Domain: Add Value (see example in text box)
- Process: Add Value (see example in text box)
- Hash: Add Value (see example in text box)
-
Device: Choose to exclude device by Type or Specific Type
- If you've chosen Type:
- Select the desired category (CD/DVD or Removable drives)
- Select the desired Bus (Any, ATA IDE, Firewire, SCSI, USB, PCMCIA)
- If you've chosen Specific Type:
- Select the desired category (CD/DVD or Removable drives)
- Add value to Hardware ID (see example in text box)
- Add value to Serial ID (see example in text box)
- If you've chosen Type:
Hardware ID and Serial ID details can be copied from the Device Control Report and pasted here to add an exclusion for a specific device. This is helpful when you've set a broad Device Control policy to block all removable drives but still require at least one particular endpoint to access USB Flash drives.
- Click Add
- Click Scope on the light-blue menu and select Site or Policy
- If selecting Policy, it's important to note that if no policies are associated with your Exclusion List, then no endpoints will be affected—to associate a policy with your Exclusion List, click Edit Policy Associations

- You will see a popup that allows you to choose which policies you want to associate with your Exclusion List
- Once you select the desired policies, click Update
- If selecting Policy, it's important to note that if no policies are associated with your Exclusion List, then no endpoints will be affected—to associate a policy with your Exclusion List, click Edit Policy Associations

Mac
When creating an Exclusion List for endpoints running macOS, you can exclude files based on filename and filepath. You can also select the scope of your Exclusion List, choosing Site, meaning the list will apply to all of your Mac endpoints at the site-level, or Policy, meaning the list will apply only to endpoints that belong to any policies you've selected to be associated.
- Click +Add Exclusion at the top-right corner of the screen
- Choose a Subtype (Filename or Filepath), and add Value (see example in text box)
- Click Add

- Click Scope on the light-blue menu and select Site or Policy
- If selecting Policy, it's important to note that if no policies are associated with your Exclusion List, then no endpoints will be affected—to associate a policy with your Exclusion List, click Edit Policy Associations

- You will see a popup that allows you to choose which policies you want to associate with your Exclusion List
- Once you select the desired policies, click Update
- If selecting Policy, it's important to note that if no policies are associated with your Exclusion List, then no endpoints will be affected—to associate a policy with your Exclusion List, click Edit Policy Associations
Linux
When creating an Exclusion List for endpoints running Linux, you can exclude files based on filename and filepath. You can also select the scope of your Exclusion List, choosing Site, meaning the list will apply to all of your Linux endpoints at the site-level, or Policy, meaning the list will apply only to endpoints that belong to any policies you've selected to be associated.
- Click +Add Exclusion at the top-right corner of the screen
- Choose a Subtype (Filename or Filepath), and add Value (see example in text box)
- Click Add

- Click Scope on the light-blue menu and select Site or Policy
- If selecting Policy, it's important to note that if no policies are associated with your Exclusion List, then no endpoints will be affected—to associate a policy with your Exclusion List, click Edit Policy Associations

- You will see a popup that allows you to choose which policies you want to associate with your Exclusion List
- Once you select the desired policies, click Update
- If selecting Policy, it's important to note that if no policies are associated with your Exclusion List, then no endpoints will be affected—to associate a policy with your Exclusion List, click Edit Policy Associations
Isolation
Isolation Exclusions are specialized rules that allow a device to keep communicating with specific services even while it is Isolated from the network. This is helpful when you want to allow a Remote Desktop or SSH connection, or even just ensuring the VIPRE Cloud Agent can still communicate with your Endpoint Security web console.
- Name your Isolation Exclusion
- Select if you want Both directions, only Inbound, or only Outbound
- Enter the local port number to use on the isolated devices
- (Optional) Enter the remote port number to use on other computers
- If you want isolated devices to be able to communicate with a specific computer, enter its remote IP Address here
- Click Add (or Update if editing an existing Isolation Exclusion)

Incidents
This feature requires a VIPRE EDR or EDR+MDR subscription and VIPRE Cloud Agent for Windows v13.4 or higher. Support for macOS and Linux is coming soon.
Incident Exclusions provide granular control over EDR detections to reduce false positives and "noise" while keeping your critical defenses active and unhampered.
Important: Incident Exclusions apply only to detections that originate from the EDR engine. Incidents triggered by other security components will still be reported and will not be excluded.
Use Case: Managing Administrative Scripts
An automated backup script triggers a security incident when it uses reg.exe to perform a registry dump. To prevent future false positives without broad exclusions, an administrator creates an Incident Exclusion targeting the specific file path and process name associated with the backup tool. This ensures the known-safe script runs smoothly while the EDR engine continues to monitor for unauthorized or suspicious uses of reg.exe elsewhere.
To add an EDR Incident Exclusion, perform the following steps within the VIPRE web console:
- Navigate to MANAGE > Exclusions, then click Incidents
- Click Add Exclusion List in the top right corner
- Name your custom exclusion list and click Next
- In this example, we've named our list EDR Incidents
- On the Rules tab, you'll see two options: Freeform and Builder
- 📌Pro-tip: Be as specific as possible—e.g., when looking at INVESTIGATE > Incidents, you can examine the Root Cause Analysis to identify the trigger node (the specific event that caused the incident) and determine the most specific exclusion criteria, like process path, process name, command line, etc.

|
 |
- If using Freeform, click in the text box and select your criteria

- If using Builder, click the + to select Add Rule or Add Group

- Select your criteria from the dropdown
- Choose an operator: Equals, Does Not Equal, or Starts With
- Type (or paste) the details as required
- Click Add
- Click Scope

- Select Site or Policy
- 📌Pro-tip: Use Site when the exclusion should apply to every device; use Policy when the exclusion is intended for specific agents or policies—creating an exclusion with scope set to Policy without actually assigning it a policy will result in the exclusion list not being active
- To associate a policy with your Exclusion List, click Edit Policy Associations

- You will see a pop-up that allows you to choose which policies you want to associate with your Exclusion List
- Once you select the desired policies, click Update
- Click Create in the top right corner to save your new Incident Exclusions list
Manage Exclusions:
Within the custom exclusion list, you can select the exclusion category type from the side navigation menu. Find the desired exclusion and select the Modify or Delete icons.
